Watch our Explainer video and learn more about RPaaS.
Why choose InterVision’s RPaaS?
InterVision’s Ransomware Protection as a Service (RPaaS) is the industry’s first and only holistic approach to ransomware threats, focused on the entire lifecycle of detection, protection, and recovery
- Most comprehensive approach available
- Backed by industry leading SLAs
- Trusted leader in data recovery
InterVision Cybersecurity Solutions
As cyber threats continue to grow in number and sophistication, it’s important to have the right level of protection in place. We offer three levels of cybersecurity solutions. Use our chart to compare features and find the right fit for your business.
Foundation | Professional | Enterprise | |
Builds a solid foundation for detection, and response to Cyber Threats. | Improves upon IV cybersecurity foundation by validating your cybersecurity plan and providing 24x7x365 professional remediation of vulnerabilities. | Adds to the IV cybersecurity professional offering with comprehensive and ongoing security posture management and recovery services to end downtime risk. | |
Managed Detection and Response (MDR) |  |  |  |
Incident Response (IR) Retainer |  |  |  |
Penetration Testing |  |  (1-time) |  (Continuous) |
Enhanced Cyber Threat Concierge Service |  |  |  |
Monthly vCISO |  |  |  |
Managed Device (Monitoring, Patching, Remediation) |  |  |  |
Managed Helpdesk |  |  |  |
Endpoint Detection and Response (EDR) |  |  |  |
Disaster Recovery as a Service (DRaaS) |  |  |  |
A real-time customer attack recovered in 67-minutes
This real-time attack and recovery timeline below from one of our clients exemplifies how RPaaS broke recovery barriers and provided true RTO exceeding expectations.
-
-
-
-
-
-
NOTE
NOTE
OPTIONAL capture of forensic data for analysis prior to recovery operations, dictated by legal counsel
-
-
6:30AM
6:30AM
Infected data recovered from immutable repository at recovery point before incident – scanned and confirmed clean
-
Fortify
Fortify
Security posture reviewed with client and a recommendation is made to geofence firewalls and block PowerShell via GPO
-
Outcomes
Detect and Protect:
Attack identified within 5 minutes. Full report with remediation recommendations to client within 25 minutes.
Respond and Recover:
Compromise contained and 40TB file server restored in under 10 minutes after receiving client go ahead.
Advise and Adapt:
Client environment hardened against future attacks based on post-mortem findings.
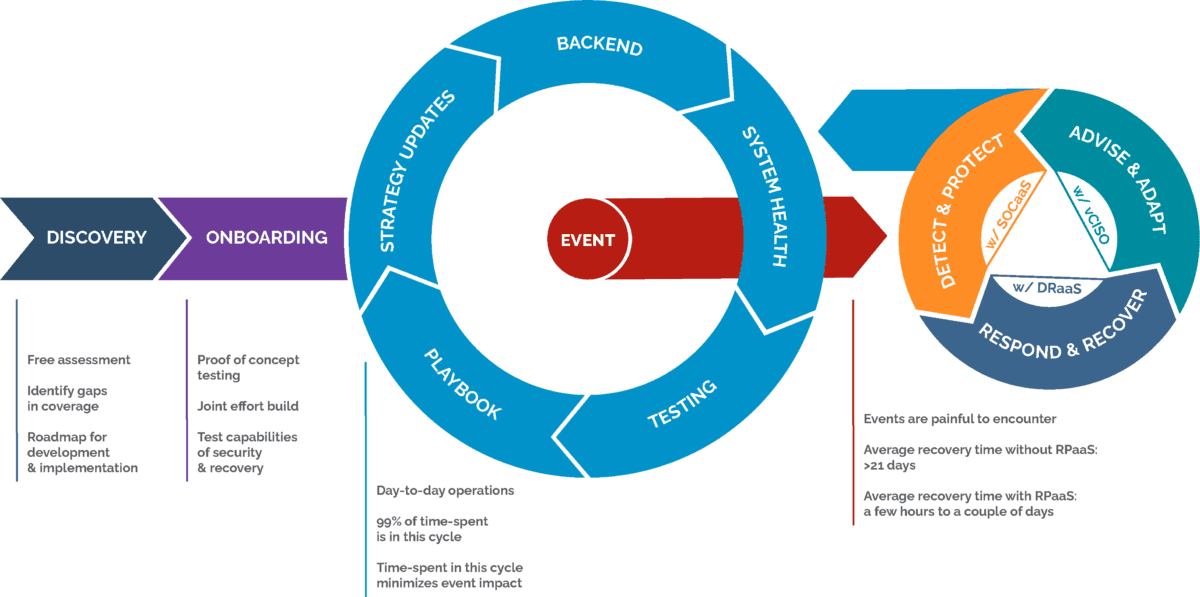
The RPaaS process
The RPaaS process is a proven comprehensive approach that is backed by industry-leading SLAs that support your business requirements.
WHITE PAPER
Ransomware puts your company in triple jeopardy
The costs can be astronomical without proper planning. Learn how these cyber criminals work to hit you more than once and how to identify and fill the gaps in your ransomware strategy.
Our experts have compiled research and recommendations to help you better understand threats, protection, and solutions.Knowledge is power
Benefit from a comprehensive approach with maximum protection and minimum disruption.
Discover how we can help you transform your business with innovative solutions and exceptional service.
Begin your journey now >























